|
Firmware available for download on downloads tab above.
K5_P6 Update – 5-Nov-2021: NOTE: For use with “LX-800” CPU (C3414) ONLY. Will not work with 5X86 (C3413) or 486 and disk on chip configuration (C3412). Operating System Must update OPERATING SYSTEM to use this update! NOTE: Due to California 2020 cyber-security regulations, users must immediately change the user access account from the default using the Sage User Manager tool. The user account file named “Schneider_Electric_1_USERS.tar.gz” located in the “FW_Update/Secure/updateGen” directory, only has up/download permission to enforce this policy, is delivered on new RTUs and installed when using the Initial Installer to convert a G3_P6 or earlier revision. The user account file named “Schneider_Electric_2.tar.gz”, located in the same path, has the old default “Admin” credentials. Use this user account file at your own risk. Fixes: Command Log: Fix issue with large number of old command log files causing CPU performance to degrade on startup as command log filenames get cataloged and listed into download menu. Very disk intensive process caused slowdown in GUI performance and configuration downloads. New limit imposed on number of command log files 744 files - 31 days of command log files created once per hour (24 * 31) - is enforced at startup. NOTE: Download any unsaved Command Log files prior to this update. Automatic enforcement of new limitation on number of files may cause unsaved Command Log files to be deleted at startup.
0 Comments
The latest firmware is available for download on the Downloads tab above.
Update: The SAGE Team is proud to announce the release of our latest firmware release for the SAGE RTU product family. There are many important security enhancements, including this VxWorks Urgent/11 fix, and exciting features included in this release. For more details about the release, see our post here. Schneider Electric is aware of recently disclosed vulnerabilities in Wind River’s VxWorks TCP/IP Stack. These vulnerabilities have wide-ranging impact across multiple IT and industrial applications. We are working closely with Wind River to understand and assess how these vulnerabilities impact Schneider Electric offers and our customers’ operations. We downloaded Wind River’s patches as soon as they were made available to us, and we have quickly instituted a remediation plan to evolve all current and future products that rely on the Wind River platform to embed these fixes. We will continue to monitor and will respond further if new information becomes available. In the meantime, customers should immediately make sure they have implemented cybersecurity best practices across their operations to protect themselves from these vulnerabilities. Where appropriate this includes locating your industrial systems and remotely accessible devices behind firewalls; installing physical controls to prevent unauthorized access; and preventing mission-critical systems and devices from being accessed from outside networks. Please subscribe to the Schneider Electric security notification service to be informed of updates to this disclosure, including details on affected products and remediation plans, as well as other important security notifications: https://www.schneider-electric.com/en/work/support/cybersecurity/security-notifications.jsp www.schneider-electric.com/en/work/support/cybersecurity/security-notifications.jsp For additional information and support, please contact your Schneider Electric sales or service representative or Schneider Electric’s Customer Care Center. An update for our customers regarding the recently announced Urgent/11 VxWorks vulnerabilities. We are aware of the vulnerabilities and working to include the patches for these vulnerabilities in our SAGE RTU operating system. We are committed to the security of your equipment and will release a patch as soon as possible. These vulnerabilities are all related to the TCP/IP network stack. If your RTU is not connected to one of the ethernet ports, which could possibly be accessed from a network, there is no additional risk associated to these devices. Only network connected devices are affected by these vulnerabilities. Serial connections are not affected. These patches will be included in our next firmware release, C3414-500-S02K4, which will include this and other exciting features like RADIUS authentication, and some excellent improvements to our SEL Relay interoperability. Keep an eye out for the firmware release here. If you have any questions, feel free to contact me. See the official announcement for all Schneider Electric products here. https://www.schneider-electric.com/ww/en/download/document/SESB-2019-214-01
The SAGE Team is proud to announce the release of our latest firmware release for the SAGE RTU product family. There are many important security enhancements and exciting features included in this release. See below for more details. The C3414-500-S02K4 firmware can be downloaded from our Downloads -> Firmware Tab or by clicking here. Firmware Highlights
On July 16th, 2019 the North American Electric Reliability Corporation (NERC) issued a Recommendation to Industry addressing supply chain concerns regarding certain Chinese suppliers. Use of products and services from these suppliers represents a tangible risk to the Bulk Electric System.
NERC has required many of our customers to respond regarding the status of our activities in relation to NERC's recommendation. This post serves to provide the status of SAGE RTU's regarding these suppliers.
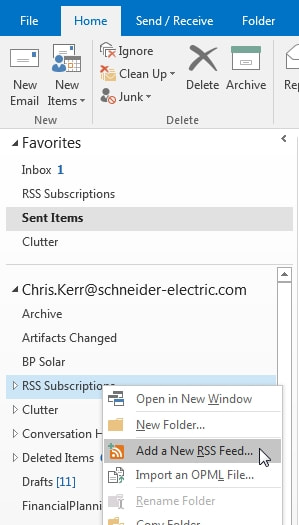
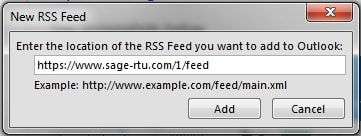
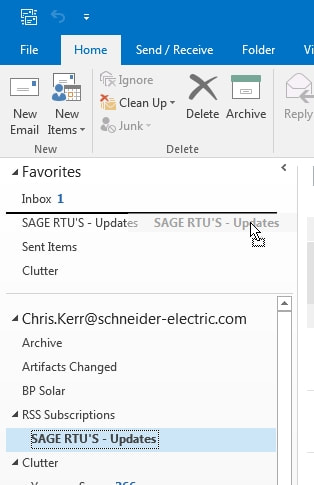
No components in our SAGE RTU's are sourced from any of the companies in the list above or the attached PDF. This includes our RTU baseboards, I/O Expansion PCB's, the C3414 CPU, and any PC104 Expansion boards. Please contact us if you have any follow up questions regarding our products. Fast and Easy Steps below.All of the posts from this page will show up in your Outlook client, including our Monthly Cybersecurity Updates, Product Announcements, and other News.
3. (Optional) Add the RSS Feed to your Favorites for quick access.
C3414-500-S02K3 Firmware Available for DownloadThe new firmware can be downloaded on the Downloads section of this website. For use with the red C3414 (LX-800) CPU. Will not work with previous CPU hardware versions. Enhancements:
Starting January 2018, the Secure Firmware will ship with every SAGE RTU.That’s a good thing. The Secure Firmware includes everything from the legacy firmware with lots of improvements. Download the Secure Firmware Announcement here. |
Categories
All
Archives
July 2024
|
||||||||||||||||||||
Services |
Company |
|

 RSS Feed
RSS Feed